Home Security Lab
This Home Security Lab serves as a dedicated environment for hands-on technical research, where I bridge the gap between theoretical security concepts and practical implementation. By simulating real-world network architectures and deploying various defensive and offensive security tools, I use this space to rigorously test system vulnerabilities, automate monitoring, and refine incident response protocols. The following documentation outlines the lab’s configuration and the specific projects I have conducted to stay at the forefront of the evolving threat landscape.
The Architecture
1. Virtualization & Infrastructure
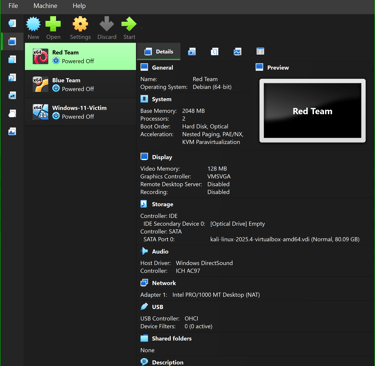
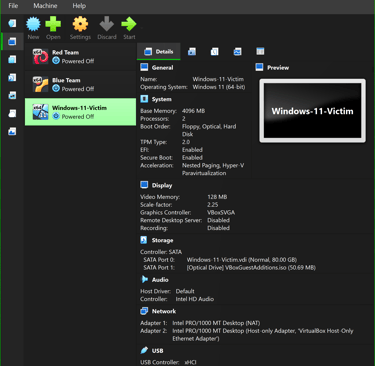
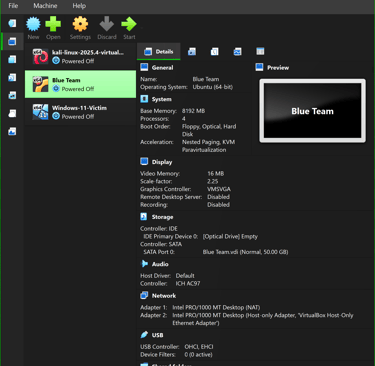
Hypervisor: I utilize Oracle VirtualBox 7.0+ to manage a local cluster of virtual machines, allowing for rapid snapshotting and rollback during malware analysis.
Components: The lab runs on a three-node architecture: a lightweight Ubuntu Server (SIEM), a Windows 11 Enterprise endpoint (Victim), and Kali Linux (Attacker), all hosted on a custom high-performance workstation.
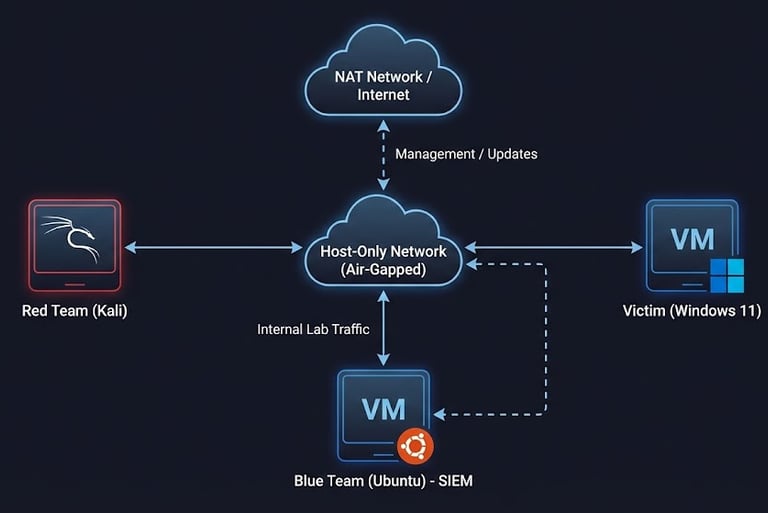

2. Networking & Segmentation
Isolation: Instead of traditional VLANs, I utilize VirtualBox Host-Only Networks to create a strictly air-gapped environment. This ensures that live malware detonations and brute-force traffic are physically unable to leak onto my home production network.
Dual-Homing: The SIEM server is configured with a dual-adapter setup (NAT + Host-Only), allowing it to ingest internal logs from the isolated lab network while maintaining secure access to external repositories for threat intelligence updates.
3. Defensive Stack (Blue Team)
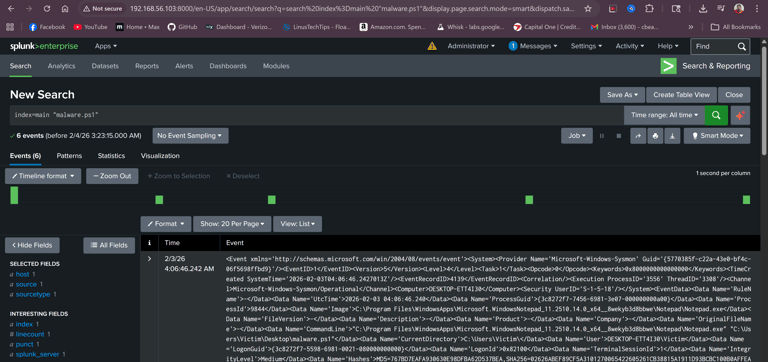
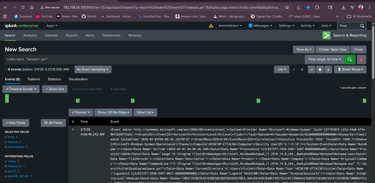
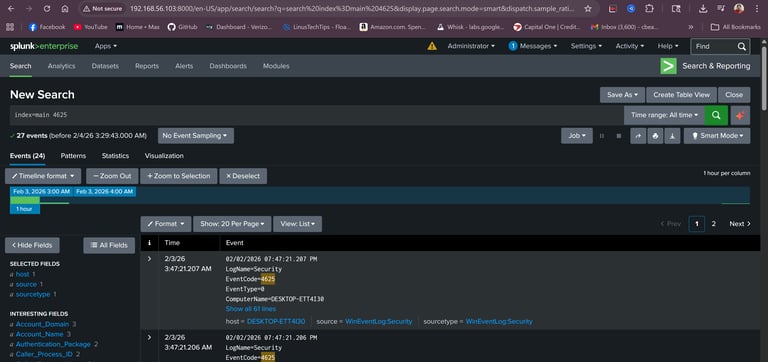
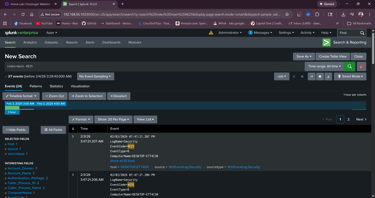
SIEM/Log Management: Splunk Enterprise serves as the central nervous system of the lab, ingesting and indexing real-time data from the victim endpoints.
Endpoint Telemetry: The Windows victim is enhanced with Sysmon (using the SwiftOnSecurity configuration) to capture high-fidelity logs that standard Event Viewer misses, such as process creation (Event ID 1) and file creation (Event ID 11).
Log Forwarding: A Splunk Universal Forwarder is deployed on the endpoint, configured to bypass local permission restrictions and pipe "Audit Failure" and "Sysmon" logs directly to the SIEM.
4. Offensive & Testing Tools (Red Team)
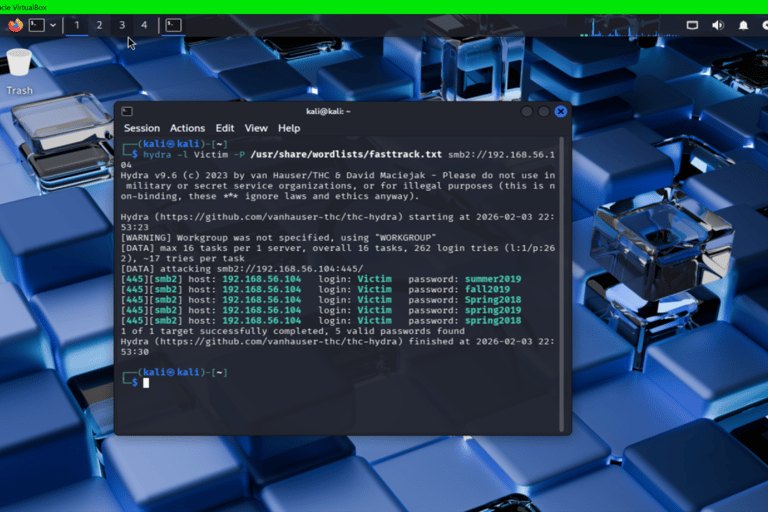
Attack Platform: A dedicated Kali Linux instance serves as the primary workstation, equipped with Hydra for network-based credential attacks (specifically targeting SMBv2) and smbclient for manual enumeration.
Malware Simulation: I develop and deploy custom PowerShell scripts to simulate ransomware behavior, specifically testing the Blue Team's ability to detect mass file modification and "ransom note" creation artifacts in real-time.


Project Reports
Detailed write-ups of the infrastructure build and attack analysis.
The Build Guide: A step-by-step breakdown of the VirtualBox, Splunk, and Network configuration used to create this air-gapped lab.
Purple Team Report: A full incident report covering the Hydra brute-force and PowerShell ransomware simulation, including root cause analysis and detection logic.
Contact
Reach out to discuss projects or collaborations
Phone
+1-520-396-8305
© 2026. All rights reserved.
